The $3 Trillion Problem Nobody Talks About
Real World Assets (RWAs) are the next frontier of DeFi. Tokenized treasuries, real estate, private credit — the promise is bringing trillions in traditional assets on-chain. But here's the uncomfortable truth: most RWA protocols today are just trust wrapped in blockchain aesthetics.
When a protocol claims "$500M in reserves backs our token," what's actually verifying that? In most cases: a PDF from an auditor, updated quarterly, with a 90-day lag. That's not verification — that's hope with extra steps.
The crypto industry learned this lesson the hard way. FTX had auditors. Celsius had auditors. Terra had... well, math that didn't add up. The common thread? Verification was delegated to trusted third parties who either couldn't or wouldn't catch problems in real-time.
The Current "Proof of Reserves" Landscape
Let's be honest about where the industry stands today:
Every single approach above has the same fundamental weakness: at some point, you're trusting a human or institution not to lie.
And that's the gap AFI set out to close.
What If You Could Remove Trust Entirely?
What if instead of trusting an auditor, a data provider, or a protocol team, the proof itself was the guarantee? Not "we promise the data is correct" but "here's a cryptographic proof that the data was computed correctly inside tamper-proof hardware, and here's a zero-knowledge proof that the math checks out — verify it yourself."
That's exactly what AFI's attestation pipeline does. It combines three technologies that, individually, are powerful — but together, create something no single approach can achieve:
- Trusted Execution Environments (TEE) — Hardware that proves what code ran
- Merkle Tree Commitments — Cryptography that proves what data was committed
- Zero-Knowledge Proofs (ZKPs) — Mathematics that proves computations are correct without revealing private data
The Architecture: Hardware + Cryptography + Math
Here's how AFI's pipeline works end-to-end:

Legend: Orange-bordered = key aggregation points | Green-bordered = verification outputs | The middle section (Salt Derivation through ZK Proof Generation) runs entirely inside the AWS Nitro Enclave.
Let's break down why each layer matters — and why you need all three.
Layer 1: Trusted Execution Environments — Proving What Code Ran
A Trusted Execution Environment is a hardware-isolated computing environment. Think of it as a sealed room where code runs, and even the server operator can't peek inside or tamper with the execution.
AFI uses AWS Nitro Enclaves — isolated virtual machines with no persistent storage, no external networking, and no admin access. When code runs inside a Nitro Enclave, AWS hardware produces an attestation document: a cryptographic certificate that says:
"This specific code (measured by hash) ran inside genuine AWS hardware, and it produced this specific output."
The attestation is signed using ECDSA P-384 with a certificate chain that traces back to AWS's Root Certificate Authority. To forge this signature, an attacker would need to compromise AWS's root cryptographic keys — the same keys that secure AWS's entire cloud infrastructure.
What competitors miss: Most TEE-based systems sign data outside the enclave, or use the TEE attestation as a generic "this code ran" stamp. AFI does something fundamentally different — the Merkle root of all committed data is embedded directly as the user_data field inside the hardware attestation. This means the attestation and the data proof are cryptographically inseparable. You can't forge one without breaking the other.
Layer 2: Merkle Commitments — Proving What Data Was Used
Every piece of data — each reserve balance, each liability — gets individually committed using cryptographic hash functions. The process:
- Each value gets a unique salt — derived deterministically so the same input always produces the same commitment, but an outsider can't reverse-engineer the value
- Each value is hashed with its salt — creating a commitment that hides the value but can be revealed later for auditing
- All commitments are combined into a Merkle tree — producing a single root hash that represents the entire dataset
This Merkle root is the fingerprint of the entire attestation. Change a single digit in any reserve balance, and the root changes completely. It's collision-resistant — finding two different datasets that produce the same root is computationally infeasible.
Why this matters for privacy: Individual reserve breakdowns (which custodian holds how much, which chain has what liability) remain private. Only the cryptographic commitments are public. But if an auditor or regulator needs to verify a specific value, the protocol can selectively reveal that single commitment without exposing everything else.
Layer 3: Zero-Knowledge Proofs — Proving The Math Is Right
Here's where it gets powerful. ZK proofs let AFI prove statements about the data without revealing the data itself:
- "These 12 reserve values sum to exactly $500M" — proven without revealing any individual reserve amount
- "These 8 liability values sum to exactly $400M" — proven without revealing any individual liability
- "The Merkle root was correctly computed from these leaf commitments" — proven without revealing the leaves
AFI uses Groth16 proofs on the BN128 curve — the same proof system used in production by Zcash and many Ethereum L2s. These proofs are:
- Succinct: ~192 bytes regardless of how much data is being proven
- Fast to verify: Three pairing operations, verifiable on-chain in a single transaction
- Sound: Breaking the proof requires solving the discrete logarithm problem — believed to be computationally infeasible
Why You Need All Three (And Why One Isn't Enough)
Here's the critical insight: each technology alone has a gap. Together, they close every gap.
The Secret Weapon: Timeseries Chaining
There's one more piece that most attestation systems miss entirely: temporal integrity.
Even with perfect cryptographic proofs, what stops a protocol from showing you an old proof when the current state is worse? Nothing — unless you chain attestations together.
AFI links every attestation to the previous one using cryptographic chaining:
Attestation #1: Root₁
Attestation #2: Hash(Root₁ ‖ Root₂)
Attestation #3: Hash(Hash(Root₁ ‖ Root₂) ‖ Root₃)Each new attestation is mathematically dependent on every previous one. You can't skip, reorder, or replace any attestation in the chain without breaking the entire sequence. This creates a blockchain-like immutable history of every proof ever generated — making rollback attacks impossible.
What a Verifier Actually Sees
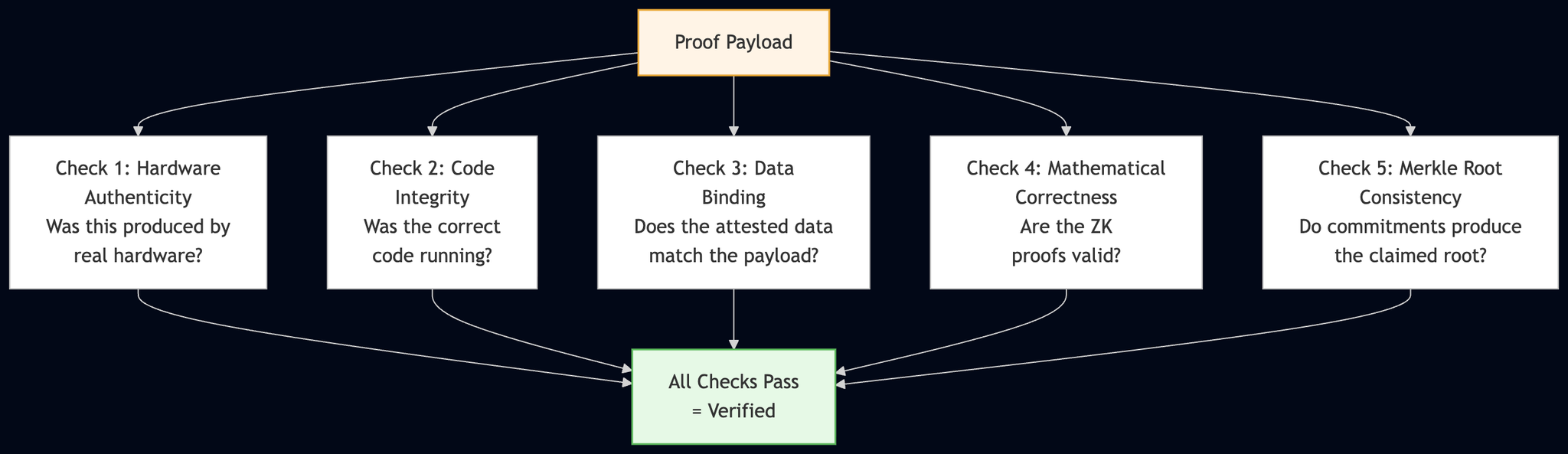
When someone verifies an AFI attestation, they check:
- Hardware Authenticity — The attestation document's certificate chain traces to AWS's Root CA. This proves the code ran inside real AWS Nitro hardware.
- Code Integrity — PCR values (Platform Configuration Registers) match the expected measurements. This proves the exact expected code was executed — not a modified version.
- Data Binding — The Merkle root inside the hardware attestation matches the root computed from the field commitments. This proves the attested data is exactly what the hardware processed.
- Mathematical Correctness — The ZK proofs verify against the public signals. This proves the reserves sum to the claimed total, the liabilities sum to the claimed total, and the Merkle root was correctly computed.
- Historical Continuity — The chained root matches the chain of previous attestations. This proves no attestation was skipped or replaced.
And here's the key: anyone can do this. The verification payload is self-contained — it includes the AWS Root CA certificate, the ZK verification keys, and all the data needed to verify. No special access required. No API calls to the protocol. No trust in anyone.
How This Compares to What Exists Today
The Bigger Picture: Why This Matters for DeFi
RWA protocols are asking users to bridge the trust gap between traditional finance and decentralized systems. That bridge can't be built on the same trust assumptions that DeFi was created to eliminate.
When a user locks capital into a tokenized treasury product, they deserve more than "an auditor checked this last quarter." They deserve:
- Real-time proof that reserves back the token
- Mathematical guarantees that the numbers add up
- Hardware attestation that the code computing these proofs wasn't tampered with
- Historical proof that the protocol has been continuously solvent
- The ability to verify all of this themselves without trusting anyone
That's what AFI delivers. Not "trust but verify" — just verify.
What's Next
AFI is building toward a future where every RWA protocol can generate verifiable, self-contained cryptographic proofs of their reserves — updated continuously, verified by anyone, trusted by math.
The infrastructure is live. The proofs are real. And for the first time in DeFi, "proof of reserves" actually means proof.





%202.png)
.svg)

